For founders, CEOs, and CTOs, the conversation around AI has moved into a more operational territory. Now, the focus is no longer on what models can generate in isolation, but on whether they can participate in real workflows — reducing the friction that accumulates across tools, handoffs, and recurring processes.
OpenClaw sits directly in this shift. Its relevance is not in novelty or experimentation, but in how it exposes a different direction for software: systems that don’t just assist, but interact with the flow of work. With over 247,000 stars on GitHub as of early 2026, it has moved beyond early curiosity and is now being explored by teams in both Silicon Valley and China as a way to connect communication layers with operational systems.
For business leaders, that makes the central question more practical and more demanding. The value of an agent is defined by whether the workflow is important enough to justify automation, structured enough to benefit from it, and controlled enough to fail safely. That is the real lens for evaluating OpenClaw: not “what can the agent do?” but “which workflows are valuable enough to automate and important enough to control?”
How We Chose These OpenClaw Case Studies
This list was built to identify the workflows that are most relevant to business leaders evaluating where autonomous AI may create real operational value.
To keep the analysis useful, we applied four selection filters to every example:
- Business value — does this solve a real operational problem?
- Transferability — could this realistically fit into a company workflow?
- Documentation quality — is there credible public evidence behind it?
- Guardrail relevance — does it reveal something about control, risk, or system design?
Once selected, each case was then evaluated based on the type of evidence supporting it.
The examples in this article fall into three evidence categories:
- Official implementations — documented in OpenClaw’s showcase or core materials
- Community workflows — real-world usage patterns reported by developers and advanced users
- Market signals — independent reporting that shows broader adoption and industry movement
These case studies should be read as documented implementations and emerging workflow patterns, not as universal proof of enterprise maturity. They are most valuable as signals of where OpenClaw-style systems are beginning to create practical value, and where the need for architecture, governance, and guardrails becomes impossible to ignore.
Case Study 1: Slack Auto-Support for Internal Ops and Incident Response
One of the most operationally relevant examples of OpenClaw in practice comes from a Slack Auto-Support workflow documented in the project’s official showcase. Among publicly available use cases, this is one of the clearest examples of an agent participating in internal operations rather than simply assisting with isolated tasks.
What the workflow does
The agent monitors specific company Slack channels, such as #ops-triage or #internal-support. It identifies incoming requests, provides helpful responses based on internal documentation, and forwards high-priority notifications to a secondary channel like Telegram. In one documented instance, an OpenClaw agent autonomously identified and suggested a fix for a production bug in a deployed application without being prompted by a human.
In documented examples, the agent has identified issues within a conversation thread and proposed potential fixes within the workflow, effectively acting as an additional layer of operational awareness inside the communication system.
Why does this create business value
This workflow targets the "support load" on senior engineers. By reducing the time required to triage and escalate issues, the agent helps compress response loops without requiring constant attention from senior engineers.
The value of this workflow is that it turns Slack from a passive communication layer into an active operational surface, where signals are interpreted and routed in near real time.
Best fit
This pattern is most effective in environments where Slack is already a central coordination layer and where internal knowledge, such as runbooks, documentation, or past resolutions, is sufficiently structured for the agent to reference.
It is particularly relevant for engineering-heavy startups, product-led companies, and internal operations teams with high communication volume.
Where it breaks
The primary risk in this workflow is excessive action scope. Monitoring and responding within Slack is relatively low risk, but the moment the agent is allowed to trigger actions in downstream systems, such as merging code, updating infrastructure, or initiating deployments, the failure modes become significantly more serious.
A misinterpreted message, an ambiguous request, or a malicious prompt could result in unintended actions being executed with privileged access. OpenClaw’s threat model highlights this as a “confused deputy” scenario, where an agent acting on behalf of a user performs operations that exceed the original intent.
This is where the distinction between assistance and authority becomes critical. The workflow becomes fragile when it is allowed to act without clearly defined boundaries, approvals, and auditability.
Case Study 2: Accounting Intake from Email and PDFs
Back-office workflows are rarely visible, but they are one of the most persistent sources of operational friction in growing companies. A documented OpenClaw implementation addresses this by automating the intake and preparation of financial documents, replacing a recurring manual coordination loop in the bookkeeping process.
What the workflow does
The agent connects to a designated email inbox, identifies incoming invoices and financial documents, parses the attached PDFs, and prepares them for a tax consultant or internal accounting system. It replaces the manual step of downloading, renaming, and sorting monthly documents.
Why does this create business value
The value of this workflow is operational rather than transformational. It removes a predictable, recurring coordination task from the monthly accounting cycle, reducing administrative overhead without requiring changes to the broader financial system.
Instead of introducing a new platform or forcing a full ERP transition, the agent operates within an existing process and smooths it. This makes it effective for teams that have already established a bookkeeping routine but want to reduce the time and attention required to maintain it.
Best fit
This pattern is most effective in environments where financial documents arrive through a centralized inbox and follow relatively predictable formats. It is relevant for SMBs, founder-led companies, agencies, and operations teams with consistent monthly bookkeeping requirements.
Where it breaks
The primary risk in this workflow is a silent failure in document processing. If the agent incorrectly parses a PDF, misclassifies a document, or fails to capture an attachment, the result may not be immediately visible but can introduce errors into the accounting process.
Security risks also remain significant. Financial documents are inherently sensitive, and routing them through external models or poorly isolated environments can expose confidential data. OpenClaw’s architecture, which processes files locally and interacts with external tools, requires careful configuration of file-system boundaries and data handling policies to prevent unintended access or leakage.
This is where the limits of automation become clear. The workflow is highly effective at handling repetitive intake and organization, but it still requires validation checkpoints to ensure accuracy. In financial processes, the cost of a quiet mistake is often higher than the cost of manual work.
Case Study 3: PR Review Feedback Through Telegram
Improving engineering throughput is not just about writing code faster, but about reducing the latency of feedback within the software development life cycle (SDLC). One of the more technically integrated OpenClaw implementations, documented in the project’s official showcase, addresses this by introducing an automated feedback layer directly into the pull request (PR) workflow.
What the workflow does
When a developer finishes a change and opens a Pull Request (PR), OpenClaw reviews the code diff and generates an initial assessment of the change. This includes identifying missing tests, flagging style or convention issues, and surfacing potential problems that should be addressed before human review.
The feedback is delivered asynchronously through a Telegram channel. It allows developers to receive immediate signals without waiting for a senior engineer to enter the review cycle. The agent acts as an early-stage filter within the process.
Why does this create business value
The value of this workflow lies in reducing review latency and improving the allocation of engineering attention. By catching straightforward issues early, it prevents senior engineers from spending time on low-level corrections and allows them to focus on architectural decisions, system design, and higher-risk changes.
This effectively adds a preliminary feedback layer to the SDLC, increasing throughput without changing the underlying development process.
Best fit
This pattern is most effective in teams that already operate with structured pull request workflows, defined coding standards, and consistent use of version control systems such as GitHub or GitLab.
It is relevant for distributed development teams and engineering-led startups that rely on asynchronous collaboration and want to reduce bottlenecks in code review cycles.
Where it breaks
The primary risk in this workflow is misplaced authority. If the agent’s feedback is treated as a definitive judgment rather than an initial signal, teams may begin to rely on it beyond its actual capability.
This can lead to false confidence, where surface-level checks are passed while deeper architectural or logical issues go unexamined. Over time, this may degrade the quality of human review rather than enhance it.
Security risks further complicate the picture. If the agent is allowed to influence merge decisions or interact with CI/CD pipelines, it becomes susceptible to indirect prompt injection. For example, malicious instructions embedded in code comments could be interpreted as actionable signals, potentially leading to unintended behavior.
Case Study 4: Local CRM and Sales Automation
Sales operations are constrained by fragmented data and inconsistent tracking. For many teams, the challenge is maintaining a reliable, up-to-date view of interactions, follow-ups, and pipeline status.
This OpenClaw pattern observed across community-documented workflows addresses this by introducing a local-first layer for capturing and querying sales activity.
What the workflow does
The agent monitors sources such as email and calendar activity to identify new contacts, track ongoing conversations, and log interactions. It stores this information in a local database, often using lightweight structures such as SQLite, creating a continuously updated record of the sales pipeline.
The agent can enrich lead data through browser-based lookup and allow users to query pipeline information using natural language. This turns scattered communication into a searchable and structured dataset without requiring manual CRM updates.
Why does this create business value
It reduces revenue-ops friction without forcing the team into bloated, high-cost SaaS stacks for simple workflows. Because OpenClaw runs locally, the business maintains total control over its customer data, which is a significant privacy advantage.
Best fit
This pattern is most effective in teams with relatively simple or mid-complexity sales pipelines, where email and calendar interactions serve as the primary source of customer data.
For founder-led sales teams, lean B2B organizations, and operators who prioritize flexibility, low overhead, and local control over standardized CRM infrastructure, this workflow is particularly relevant.
Where it breaks
The primary risk in this workflow is degradation of data reliability over time. If the agent incorrectly logs interactions, misattributes contacts, or generates incomplete updates, these errors may not be immediately visible but can accumulate into a distorted view of the pipeline.
This creates a risk of data drift, where the local system diverges from reality or from other tools used by the team. Over time, this can erode trust in the system, leading users to bypass it entirely or revert to manual tracking.
Additional risks emerge when the agent crosses from observation into action. If it initiates follow-ups, modifies records, or makes assumptions about customer intent without validation, it can negatively impact client relationships.
Case Study 5: Multi-Agent Specialized Teams and Operational Cockpits
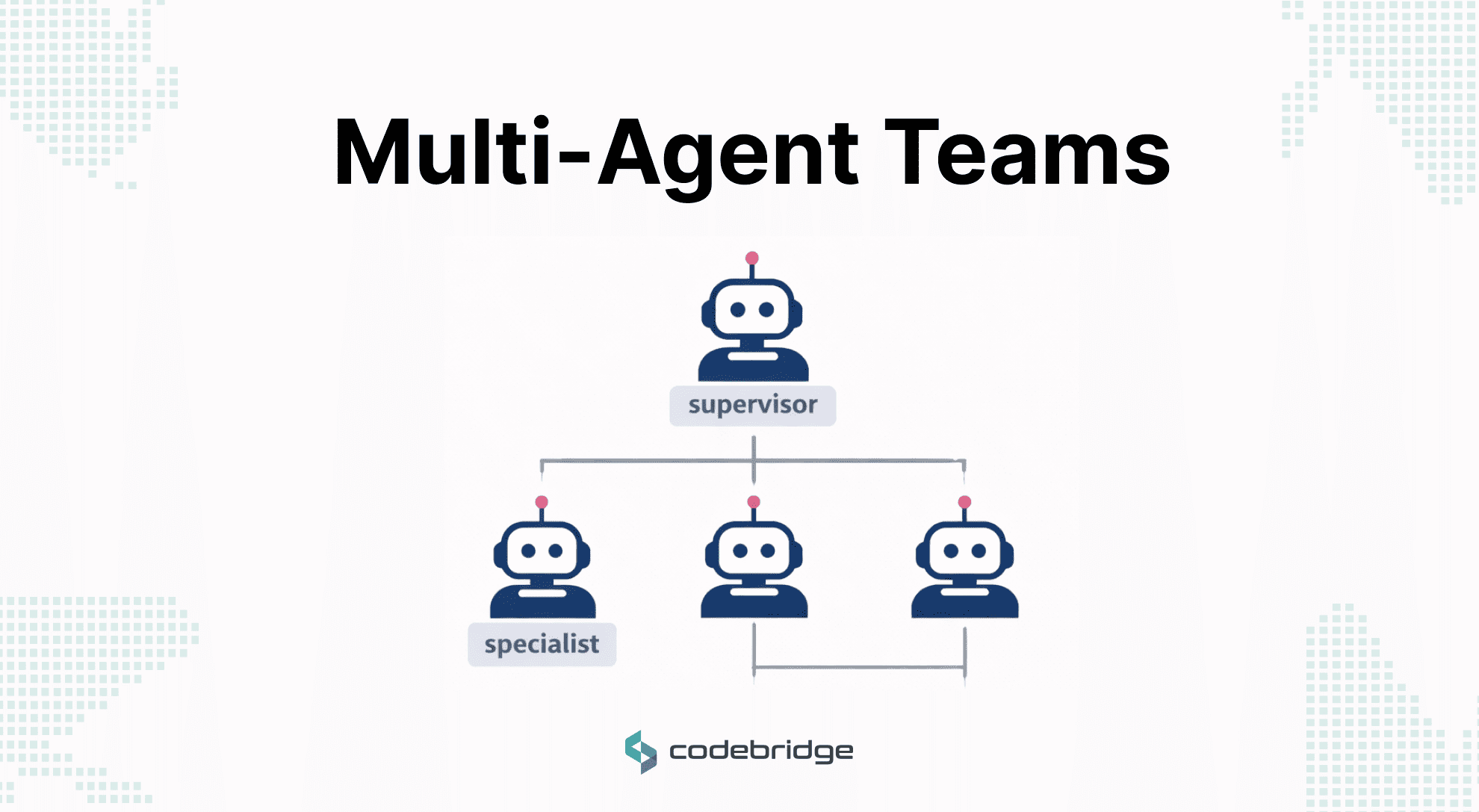
The most forward-looking OpenClaw pattern is a coordinated system of specialized agents operating as a unified execution layer. This represents a shift from tool augmentation to system-level orchestration.
What the workflow does
This involves deploying multiple specialized agents — for example, one for SEO, one for copy editing, and one for visual design — coordinated through a central "squad lead". Baidu has recently launched an entire ecosystem of "lobsters" (OpenClaw-based agents) that operate across desktop, mobile, and smart-home devices to unlock hardware-level operating capabilities.
The workflow deploys multiple specialized agents, each responsible for a narrow domain such as SEO analysis, content generation, data enrichment, or visual design. These agents are coordinated through an orchestration layer — often described as a “squad lead” — which routes tasks, manages dependencies, and aggregates outputs.
In more advanced implementations, this model extends beyond software workflows into multi-device environments. For example, large-scale deployments such as Baidu’s OpenClaw-based agent ecosystem demonstrate how coordinated agents can operate across desktop, mobile, and embedded systems to execute tasks across an integrated environment.
Why does this create business value
The value of this approach lies in delegated execution at scale as the system distributes tasks across specialized agents, each optimized for a specific function.
This enables a form of distributed problem-solving, where complex workflows are decomposed into smaller, manageable units that can be executed in parallel. For organizations, this creates leverage by augmenting them with a structured execution layer that reduces coordination overhead and accelerates output.
At a strategic level, this model begins to resemble an operational cockpit, where leaders oversee outcomes and flows rather than individual tasks, shifting management from direct execution to system design.
Best fit
This pattern is most effective in technically mature organizations that already operate with modular workflows and clear task decomposition.
It is particularly relevant for AI-native startups, internal innovation teams, and product organizations with the engineering capacity to design, monitor, and maintain multi-agent systems.
Where it breaks
The primary risk in this workflow is not failure of individual agents, but systemic failure across the orchestration layer. As the number of agents increases, so does the complexity of managing context, permissions, and interactions between components.
This creates several failure modes. Context leakage can occur when information flows between agents in unintended ways, leading to incorrect or inconsistent outputs. Permission sprawl can make it difficult to track which agent has access to which systems, increasing the risk of unintended actions. More critically, a compromised agent—through a poisoned tool, document, or input—can propagate errors or malicious behavior across the entire system.
This phenomenon, often described as cross-context attack propagation, highlights the need for strict isolation, validation boundaries, and observability across the agent network.
The workflow remains powerful when each agent operates within a clearly defined scope and the orchestration layer enforces boundaries between them. It becomes fragile when coordination complexity grows faster than governance, turning a modular system into an opaque and difficult-to-control execution environment.
The 5 OpenClaw Workflows at a Glance
Launch OpenClaw Without the Engineering Overhead
If these workflows look relevant to your business, the next question is who on your team will set this up? Non-technical founders often stall here, even when the value is clear. With our OpenClaw-based product, you can launch and test autonomous workflows without building an in-house AI platform or hiring a dedicated MLOps team. You get a ready-to-use environment where proven patterns from this article are already built in and can be configured to your specific processes, not coded from scratch.
Instead of spending months on experimentation, your team can stand up a controlled pilot in days, with enterprise guardrails already built into the system. You choose the workflows, approval logic, and data boundaries and the platform handles orchestration, monitoring, and safe execution. If you want to see how fast your organization can move from “interesting case studies” to a live OpenClaw-powered workflow, explore our product.
What These Case Studies Reveal About Enterprise-Ready Agent Design
Across these workflows, a consistent pattern emerges: the most valuable agentic systems are defined by how precisely they are constrained.
Four characteristics appear repeatedly in the implementations that create real business value:
System-spanning, not prompt-bound
The highest-value workflows extend across multiple systems — moving from communication layers to operational tools. Value does not come from generating better outputs in isolation, but from connecting fragmented parts of the business into a continuous flow.
Coordination-first, not generation-first
The strongest use cases reduce friction in handoffs, triage, and execution loops. Rather than replacing human thinking, these systems remove the overhead of moving work between people, tools, and states.
Semi-structured domains outperform open-ended ones
Workflows in finance, internal operations, and engineering support consistently perform better because they operate within defined rules and clear success criteria. Fully open-ended tasks remain far more difficult to control and validate.
Authority must lag capability
Across every case, the failure modes emerge when agents are allowed to act beyond clearly defined boundaries. Systems that assist, triage, and structure work create leverage. Systems that act without constraint introduce disproportionate risk.
This direction is already being recognized at the industry level. The 2026 launch of NIST’s AI Agent Standards Initiative reflects a broader shift toward standardizing reliability, interoperability, and governance as agentic systems move from experimental tools to always-on operational infrastructure.
Conclusion: OpenClaw Is a Signal, Not Just a Tool
OpenClaw is a commercially interesting project because it reveals which categories of work are becoming viable for agentic execution. It represents the frontier of a broader shift toward autonomous systems that act on our behalf.
However, the evidence from current implementations shows that most public examples are still early. The technology remains stochastic, and as Baidu Executive VP Shen Dou noted, agents still "make mistakes, take detours, and sometimes even complicate simple things".
For Founders and CTOs, the differentiator is implementation discipline. The real value is in the system's design required to make these agents viable in a business context. The question for 2026 is no longer whether AI agents can act; it is whether the workflow around that action is valuable enough to automate and mature enough to control.


Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
Block quote
Ordered list
- Item 1
- Item 2
- Item 3
Unordered list
- Item A
- Item B
- Item C
Bold text
Emphasis
Superscript
Subscript